I found different kinds of explanations about what Proxy ARP is, just few of them were understandable at first. After merging all of them this explanation came out of my networking workshop:
- Assuming that a router has an ARP entry of some IP address, if he receives an ARP request from somebody for that IP, the router will respond with its own MAC address.
- Proxy ARP is fairly simple technique for nodes to get MAC address of a destination host that is on a different subnet but on the same router. Same router different interface.
And this one to:
- If we have in the network one edge router that is our way out from the local LAN network. That router has Proxy ARP enabled by default. When it receives an ARP request on his interface for a client that is not actually from that local network it will try to be helpful and it will search his routing table if that network is locally connected on some other local interface. If he finds it, it will respond with his own MAC address to tell the source that he is the way to go towards that host.
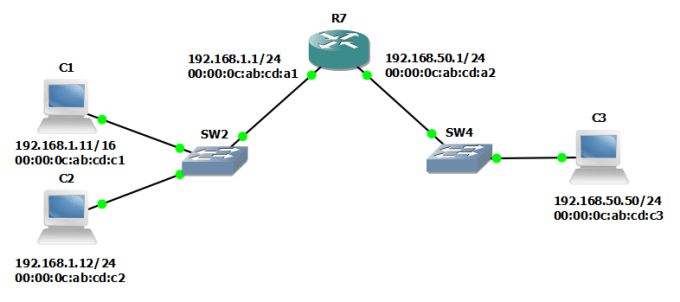
If we look at the image below, I prepared a more detailed example for those who are still a bit confused about it.
It’s a technique that enables our R7 router on the image below to proxy ARP request from C1 computer which tries to find MAC address of computer C3.
You need to note that C1 has address from /16 range and that is why it thinks that 192.168.50.50 is on the same subnet as 192.168.1.11 . If that was not the case and C1 had the address 192.168.1.11/24, it would send the ARP asking what is MAC address of default gateway. It will go to default gateway because he will know that he is not directly connected to all of network 192.168.0.0/16. We are then talking about standard routing by getting the packets from one subnet to another using routing table examination.
Proxy?
Put yourself inside Router 7.
Proxying an ARP (or some other traffic) means responding to sender (C1 in our case) faking that we are C3 (R7 fakes to be C3) and that we (R7) are the right destination of the traffic destined to 192.168.50.50. C1 then sends us all traffic for C3 and we (R7) will then forward it towards the real destination (C3) that is on our other interface.
Network device can do this Proxy ARP function pretty easily because the ARP itself works very simply.
In our example
When C1 wants to send something to C3 it will ask all his neighbours on local LAN segment where is the 192.168.50.50 by sending ARP request in form of broadcast. If the router R7 responds to this ARP request with his own MAC address of the local interface (00:00:0c:ab:cd:a1), C1 will get the response and start to talk to R7 as he is the right destination. If R7 then forwards this communication to C3 MAC address putting his local MAC address in packet as source MAC address. C3 then responds to R7 thinking he is C1 who wants to talk to him and the connection is established. C1 and C3 can speak to each other without even knowing that their traffic is being proxied on R7.
R7 will do the proxy function for ARP request if for a broadcasted ARP request that he receives, he’s having a destination IP in his routing table as a local network. By having the IP of computer C3 in it’s routing table on some other interface, it means that he can respond to C1 with his own MAC address and present himself to C1 as he is C3. It will be able, later, to forward the traffic to C3 and back from C3 to C1.
Looking inside of ARP request packets from our example
HOST C1 broadcasts an ARP request on Subnet A and ARP request packet it looks like this (it has few more fields but this is the important part):
| Sender MAC | Sender IP | Target MAC |
Target IP |
| 00:00:0c:ab:cd:c1 | 192.168.1.11 | 00-00-00-00-00-00 | 192.168.50.50 |
You see 00-00-00-00-00-00 as target MAC address in this ARP request? It means an unknown MAC address and it further means that C1 is sending this and he doesn’t know where. It then means that it will be sent everywhere on the subnet and that kind of sending it’s called broadcast. It has source MAC and IP so that potential 192.168.50.50 owner will then know to whom to respond. ARP reply is a unicast.
Router (as all other devices on subnet 192.168.1.0/24) receives the broadcast ARP request from C1. It checks out the request and it sees that the 192.168.50.50 is locally connected on another of his interfaces. It then replies to C1 with his own MAC address in the ARP reply that looks like this:
| Sender MAC | Sender IP |
Target MAC |
Target IP |
| 00:00:0c:ab:cd:a1 | 192.168.50.50 | 00:00:0c:ab:cd:c1 | 192.168.1.11 |
You see, target MAC and IP are defined with C1 addresses (it means it’s a unicast) and source MAC and IP are from R7 so he can start to be a proxy for this traffic.
When C1 receives this packet it will save the ARP record in his ARP table. For next packets destined to 192.168.50.50 C1 will not need to send ARP requests again, the ARP will be resolved from his local table until ARP record times out.
| IP Address | MAC Address |
| 192.168.50.50 | 00:00:0c:ab:cd:a1 |
There’s another thing to note here. If there would be more PCs on 192.168.50.0/24 subnet and you would check ARP cache on C1 again, you would see that his ARP cache is populated with same MAC address (the one from the router) for all PC IP addresses on subnet 192.168.50.50.
So, If on some host you see that multiple IP addresses are mapped to one MAC address (the router one) it will mean that proxy ARP is in use.
On Cisco equipment it is on by default. If you would like to disable it here is the interface level command to do that. Of course, without the “no” it will enable it again.
Router# configure terminal Router(config)# interface ethernet 0 Router(config-if)# no ip proxy-arp
But why?
If your PCs don’t have default gateway configured or they lack some basic IP routing capabilities then is the time to implement proxy arp. The good thing is that it will not disrupt any routing functions of the router nor other neighbour routers and hosts will not even know that router is there in the middle giving them the chance to talk to each other.
On the other side, it could break the communication down by filling the ARP tables of cheap end devices that have small ARP cache memory. for them, keeping more that 100-200 MAC address records for devices from other subnet could be a issue. There is also the fact that proxy arp is basically using spoofing to work and that’s bad, specially if you look from security perspective.
Thank you for your article. Maybe you are still around since 2015 🙂
Shouldn’t C3 have a default route to R7 or be in /16 instead of /24? Otherwise it’s unable to answer C1 has there’s not return path towards it.
Hi Dynek,
Yes, still around and not giving up 🙂
Here’s the deal with this example. It is an example which assumes that all those PCs have IP address and default gateway configured. The thing is that C1, with /16 subnet, will think that C3 is in the same L2 domain and it will not forward traffic towards default gateway (R7) because DG is used only if you are sending traffic outside your L2 domain. Proxy ARP on R7 will help and force C1 to use it (R7) as a next-hop by responding back to C1’s ARP broadcast because it will see 192.168.50.0/24 as another directly connected network. When ARP request from C1 is resolved, C1 can speak to C3 through R7 and TCP sessions response from C3 will get back to C1 through R7 using DG configured on C3.
Hope this helps.
Excellent! Thank you so much for your explanation. Wanted to give it a try using Mikrotik’s MetaRouter (just to understand and see it work). I’m successful now 🙂